
Biometric Verification
How to Use It for Fraud Prevention
Fraudulent activities, often targeting customers, make businesses incur losses both in reputation and finances. A significant part of combating fraud, identity theft, card payment fraud, and online money transfer fraud is ensuring customers are a true representation of who they claim to be using biometric verification.
But can biometrics serve as a critical line of action in identity theft or fraud? How can biometric systems be implemented and used? With biometric verification as a form of multi-factor authentication, a business adds an extra layer of security by checking a user’s unique biological traits. This prevents two people from representing a single person.
Here, we explore what biometric verification is, the common types, and how it prevents fraud.
What is Biometric Verification?
Biometric verification is a form of identity verification that uses the unique biometric characteristics of an individual, such as the entire face, voice, fingerprints, or irises, to identify and authenticate who they are. Since no two people have the same biological attributes, this technology proves that an individual is who they claim to be.
Biometric verification has come a long way since it was first available in the form of fingerprints. With improvements to this technology, it’s become more readily available and accessible to businesses.
Login credentials and passwords can be stolen relatively easily in today’s digital economy, but it’s difficult for fraudsters to steal, copy, or falsify an individual’s physical attributes. Since biometric verification techniques are so hard to fake, they serve as great measures for fraud protection.
How Does Biometric Verification Work?
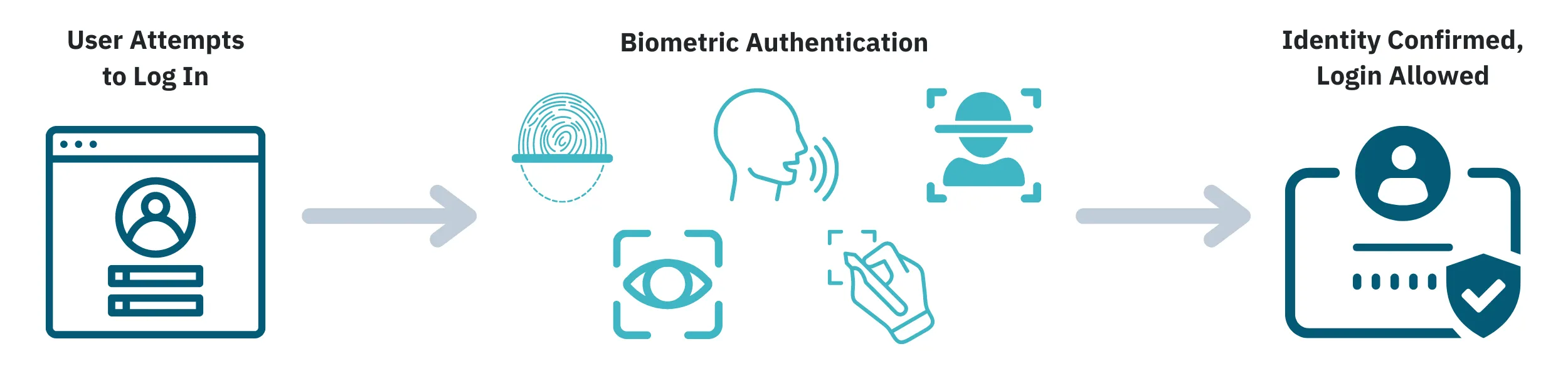
Biometric verification works by capturing and measuring biological traits unique to each person. The most commonly used traits include the face, voice, irises, or fingerprints.
There are two main methods of implementing biometric verification:
- Unimodal: A unimodal verification system authenticates a single distinct trait.
- Multimodal: A multimodal verification system authenticates two or more distinct traits.
The unimodal method offers a faster user experience with less friction. However, unimodal systems are more susceptible to cyber-attacks such as spoofing, where fraudsters are able to gain access to sensitive personal information.
Multimodal methods check two or more personal characteristics, making them much harder to bypass. While this adds an additional step for users, it provides an additional layer of security that prevents fraud from occurring.
Biometric verification works in the three simple steps outlined below.
- Enrolment: Before biometric features can be used to authenticate a user, they first need to be collected and verified. When an individual signs up on an online platform — be it a payment gateway, financial institution, or e-commerce business — they’re directed to complete the biometric verification.
- Storage: When an individual’s biometric features are captured, it doesn’t end there. These pieces of information are stored in the business’ database, so they can later be cross-referenced during authentication.
- Comparison: This is the last stage of the customer authentication process. The next time you attempt to use the platform, your present characteristics will be compared with the previous information stored in their database. This comparison determines if your authentication request will be accepted or rejected.
Overall, based on the fact that no two people have the same traits used for verification, businesses can prevent identity theft and money laundering, and keep their reputations clean.
Why Biometric Verification Is So Important
For many businesses, the use of manual verification and passwords are becoming obsolete, allowing biometric verification to take the lead. The role of biometrics isn’t just limited to the prevention of identity theft but also assists in streamlining business operations and customer trust.
Biometric verification is an ideal authentication tool because it inherently possesses numerous qualities that risk analysts look for in multi-factor authentication. The user has to possess an object — in this case, a physical characteristic — that only they would have. The user has to have an inherent quality that is fundamentally tied to who that person is — in this case, a physical attribute. The user is physically present at the location where the authentication occurs. In almost all instances of biometric verification, these three factors must be true.
Before it even authenticates a user, the nature of biometric verification makes it very difficult for bots to bypass. Since it requires an authentication of a legitimate person, it’s virtually impossible for bots to complete biometric verification, acting as a great method for preventing BIN attacks and card testing fraud.
Since biometric verification can be used to verify a user when they sign in or attempt to make a purchase, it’s an ideal preventative measure that can actually stop the fraudster before they are able to commit fraud — significantly reducing fraud losses.
5 Types of Biometric Verification
While some businesses still authenticate customers using verification codes sent to phone lines or emails, others now embrace biometric verification. This technology measures unique biological attributes that can’t be easily manipulated or faked.
There are several types of biometric verification — we cover the top five below.
Fingerprints
Biometrics have existed for a long time and are useful in security systems, forensics, and finance to verify the identity of an individual. As one of the oldest means of biometrics, fingerprints help authenticate customers by comparing the unique finger pattern with that originally stored on the platform’s database. Fingerprint verification — in addition to other security strategies — can make a platform relatively resistant to fraudulent activities.
Facial Recognition
With a global market value of over $3.8 billion in 2020, facial recognition uses the face and its part to authenticate customers. The process uses a face match algorithm to verify if the face scanned at the time of authentication matches that on record.
Fraudsters can be sneaky and capable of stealing facial identities using 2D images and 3D face renderings or masks. Interestingly, facial recognition (in addition to techniques such as 3D mapping, skin texture analysis, and 3D sensing) can prevent these spoofing attacks when fraudsters attempt to impersonate trusted entities.
Iris Scanning
New methods of biometric verification are constantly evolving. One such method is iris scanning, which involves scanning and examining the color and line pattern of the iris in the customer’s eye. This method is secure even when used as a unimodal verification system, since detection is live.
Voice Recognition
Every individual has a distinct voice and tone, and this is what voice recognition relies on. The process involves recording your voice during a normal conversation so you don’t feel the need to repeat phrases.
The recordings can be directly stored or translated into graphical templates for comparison at a later time when you need to be authenticated.
Signature & Handwriting Recognition
Signatures and handwriting recognition techniques have existed for quite a long time. The process involves scanning the signature or handwriting of a customer during verification enrolment. This method of verification, though popular, is extremely porous as it can be faked. It’s only sensible to use it in addition to other biometric or user authentication models.
How to Prevent Fraud Using Biometric Verification
As a business, having security checks such as passwords and verification software (CAPTCHA and other authentication code generators) is a great step toward ensuring the security of your platform. However, this isn’t enough.
Biometric verification, through its reliance on unique biological traits, is an important component of the multi-factor authentication process used to provide an extra layer of security to the platform. For financial institutions, eCommerce platforms, and payment gateways, biometrics don’t just prove that customers are actually who they claim to be, but also check that they’re the real holders of the cards they plan to complete transactions with.
For instance, fraudsters could be verified customers of a platform where they plan to make transactions with stolen cards. This makes it the duty of such businesses to combine biometric verification with other strategies such as transaction monitoring, activity and event monitoring, and automated surveillance to stall fraudulent transactions.
Fraudulent activities such as account takeover (ATO) fraud, online money transfer, and Bank Identification Number (BIN) fraud using brute-force computing can be limited using a combination of biometric and anti-money laundering preventive measures, as recommended by risk teams. This helps businesses keep their reputation intact and save funds that otherwise would have been used for excess chargebacks and regulatory fines.
Limit Identity Theft and Financial Fraud With Unit21
Ultimately, biometric verification is a great tool for modern customer authentication, as it’s exceedingly difficult to fake or spoof. However, it’s not the only tool at your disposal! Instead of relying solely on biometric verification, make it a core element of your fraud prevention program.
When paired with transaction and activity monitoring, robust customer onboarding workflows, and link analysis, teams will see significant reduction in fraud losses.
Schedule a demo today to learn how Unit21 can help you build a complete compliance and fraud prevention program.

