
Card Not Present (CNP)
What It Is & How to Prevent CNP Fraud
Advances in technology now allow people to make payment card transactions without their card—or even themselves—being physically present where the transaction takes place. This is a type of transaction called “card not present,” and it’s seeing widespread use due to the convenience of being able to conduct a payment card transaction from just about anywhere.
However, since a physical payment card (and sometimes the cardholder as well) isn’t present at the point of transaction, it’s more difficult to tell if the card is genuine or being used by its rightful owner. This makes CNP transactions more vulnerable to fraud than in-person transactions and has caused both merchants and financial institutions to adopt extra countermeasures against CNP-related fraud.
This article will explain what a “card not present” transaction is (and isn’t), including giving some real-life examples. It will also discuss some ways criminals use CNP to commit fraud, and how institutions that deal with payment cards can protect themselves from these types of fraud.
What is a Card Not Present (CNP) Transaction?
A card-not-present transaction is one made using a payment card such as a credit or debit card (either physical or virtual), but where the card itself does not physically interact with a terminal at the point of transaction. The transaction is completed using the payment card’s credentials only.
Card Present vs. Card Not Present
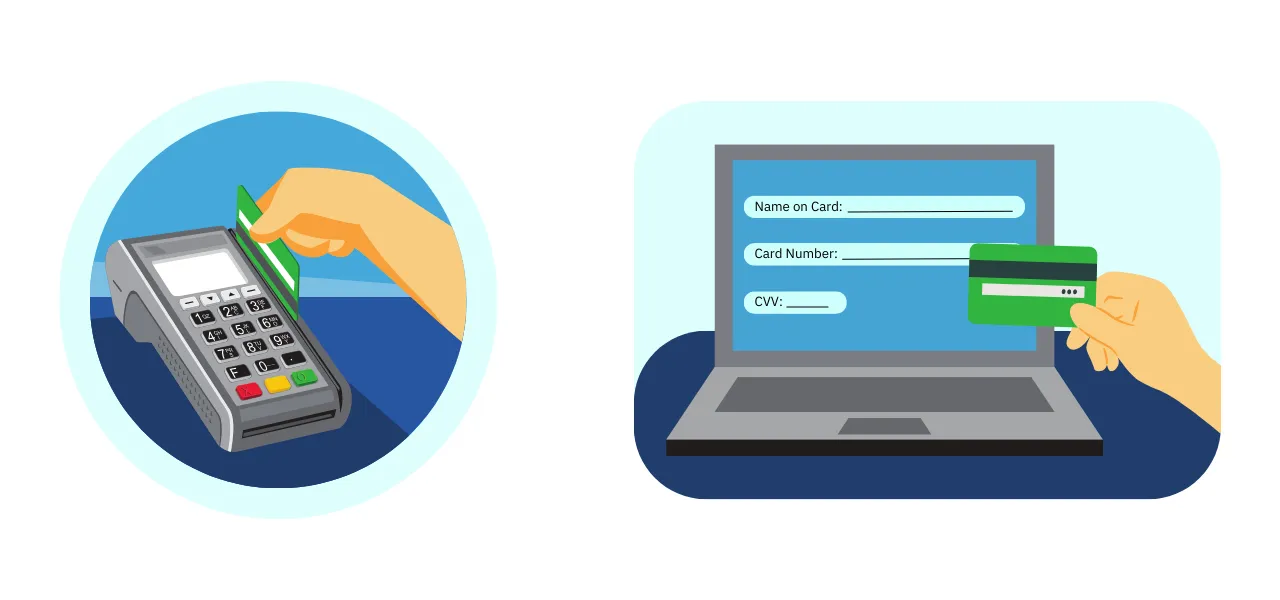
Many retail payments are card present. This is where a person goes to a physical checkout counter in a store and pays for their purchase with a payment card by physically interacting with a payment terminal. This could be swiping the card’s magnetic stripe, inserting the card (at least to have the EMV chip read), or tapping the card to transfer information via near-field communication.
Inserting a payment card into an ATM to withdraw or deposit cash, or conduct other financial business, also counts as a card-present transaction. Tapping a smartphone or other digital wallet device on a payment terminal to transfer information is also considered a card-present transaction, even though it may not involve a physical “card” per se.
A card-not-present payment happens when a person makes a purchase with a payment card, but the card itself never physically interacts with a point-of-sale terminal. Instead, providing the card’s credential information allows the transaction to go through. This includes if the cardholder is present at the point of sale, but keys in their payment card’s credentials manually.
This is the main difference between card present vs. card not present.
Examples of Card Not Present Transactions
Card-not-present transactions are easier than ever due to technological advancements, especially digital technologies such as the Internet. Thus, they are very popular because they can be conveniently conducted from almost anywhere, instead of someone needing to visit a merchant or financial institution in person. Here are some examples.
- eCommerce: A customer makes a purchase in an online store and pays for it by entering their payment card credentials into the store’s payment system. Then they either have the item delivered or pick it up at a physical store.
- Online invoices: A business client uses an online payment system to pay an invoice from the business using their payment card credentials.
- Online banking: A person uses their payment card credentials to log into an online financial dashboard and conduct transactions from there.
- Phone orders: A customer makes a purchase by dictating their payment card credentials to the seller over the phone.
- Mail orders: A customer makes a purchase by writing their payment card credentials on an order form, along with their order details, and sending it to the seller by mail.
- Card-on-file: A customer uses previously-submitted and authorized payment card details to make a purchase at a merchant, without actually needing to present the physical card. This commonly happens when a customer pays for something in installments or is paying for a recurring subscription.
Card Not Present Fraud: Common Types + How to Stay Protected
Card-not-present fraud is one of the two main types of payment card fraud, along with card-present fraud. It’s typically tougher to deal with than card-present fraud because the cardholder, the physical card, or both aren’t present at the point of transaction. This makes it more difficult to tell if the cardholder is who they say they are, or if the card is stolen or counterfeit.
What is Card Not Present Fraud?
Card-not-present fraud means using credential information from a payment card (as opposed to the physical card itself) in an unauthorized or deceptive manner. It’s becoming an increasingly popular type of fraud as more merchants accept payments not made in person, especially over digital channels.
Types of Card Not Present Fraud
The above card-not-present fraud definition is rather broad because there are several different ways fraudsters can pull the crime off. Generally, these involve accessing payment card information illegally and/or using this information to make a purchase at someone else’s expense. The following are a few specific types of CNP fraud.
- Phishing: A criminal sets up a fake website and/or sends fake messages to people to trick them into revealing their payment card credentials. Then the criminal uses these credentials to conduct fraudulent CNP transactions.
- Chargeback fraud: A criminal makes a fraudulent CNP purchase using stolen payment card credentials. Then the legitimate cardholder files a chargeback because they don’t recognize the transaction. The selling merchant loses the money and the item/service from the sale.
- Friendly fraud: Someone makes a CNP purchase, then files a chargeback after receiving the item or service. They falsely claim the product is defective or never arrived, or that the payment wasn’t properly authorized. If successful, this costs a victimized merchant the product itself, as well as its value in money.
- Triangulation fraud: A criminal sets up a fake eCommerce store, then uses stolen payment card credentials to buy items from legitimate merchants to fulfill orders. The rightful cardholder files chargebacks over unrecognized transactions, and the merchants the criminal bought from lose money and items.
- Payment card application fraud: A criminal uses fake, stolen, or synthetic identity credentials to falsely apply for a payment card to use in fraudulent CNP transactions.
Card Not Present Fraud Prevention Best Practices
It can be tricky to keep up with card not present fraud trends, as criminals are constantly coming up with new schemes as technologies and processes change. But some standard practices can help to prevent CNP fraud. Here are a few examples.
Maintain Payment Card Industry (PCI) security standards compliance
The PCI Security Standards Council consists of officials from major credit card brands. It’s responsible for setting data security standards (DSS) that any organization wanting to process credit card transactions must follow. The PCI’s current 12 main DSS standards are:
- Use firewalls to block unauthorized access to data
- Set and occasionally change secure passwords for all relevant devices
- Encrypt cardholder data with algorithms secured by encryption keys
- Only send cardholder data to known locations, and always encrypt it in transit
- Install antivirus software on all relevant devices
- Keep all relevant software on all relevant devices up to date
- Restrict access to cardholder data for entities that don’t require it
- Require unique IDs for entities that do need access to cardholder data
- Keep cardholder data in a secure physical location
- Create a log record whenever cardholder data is accessed
- Test all relevant software, physical locations, and employees for security vulnerabilities
- Document all equipment, software, and employees that can access cardholder data
Monitor transactions and data for unusual behavior
Use checkout processes and data enrichment tools to collect extra customer information such as email addresses, phone numbers, device fingerprints, IP addresses, and transaction histories. This allows for analyzing not only a particular customer’s behavior but also the whole marketplace network, for behavior that’s out of the ordinary. For example, criminals may attempt unusually low-value CNP transactions to “test” if a payment card’s credentials actually work.
Use 3DS and other multi-factor authentication
Sometimes called strong customer authentication (or SCA), 3-domain security (or 3DS), and other forms of multi-factor authentication can help stop CNP fraud by requiring customers to identify themselves in more than one way. That can include asking them something only they should know (like a one-time password), having them present something only they should possess (such as an ID document), or scanning something inherent to them (like a fingerprint). Remember how much friction this can add to a checkout process, though.
Require Card Verification Values (CVVs)
CVVs are 3-digit codes on the back of Visa, MasterCard, and Discover credit cards. They also appear on American Express credit cards but are 4 digits long and appear on the front of the card. They are not always required for credit card transactions, so they are not always included in stolen credit card credentials.
Requiring this number for a CNP payment can trip up fraudsters, since they may not know this information unless they have the actual physical card. While it’s not foolproof, it’s an added layer of security for merchants and financial institutions conducting card-not-present business. It also protects merchants from being liable for authorizing fraudulent transactions, as they’ve performed the necessary due diligence by requiring this information.
Use an Address Verification Service (AVS) system
An AVS system is a method used by major credit card companies to combat online CNP fraud. It checks whether the billing address entered for a credit card matches the address registered with that card at its issuing financial institution. AVS can be set up to automatically reject CNP transactions that fail to meet certain criteria, or simply escalate the case for investigation to let the merchant make a judgment call.
Unit21’s Tools Help Guard Against CNP Fraud
Card not present fraud prevention requires extra due diligence when verifying customer identities and watching for suspicious transactions. Make Unit21’s Transaction Monitoring and Case Management products part of your anti-fraud arsenal: aggregate and analyze both transaction data and contextual information and use it to spot shady activity or fraud trends.
Contact us for a demo, and let us show you how we can help.

