
BIN Attack
How It Works & Prevention Best Practices
The activities of fraudsters, though targeted at individuals, pose several risks for businesses globally. While financial institutions themselves aren’t the main targets of fraudsters, they can detect fraudulent activities such as a BIN attack on a victim’s account, even when the victim can’t.
But what can financial institutions and risk teams do when a BIN attack happens? Are there signs to look out for? With BIN attacks, fraudsters basically test thousands of generated credit or debit card numbers to see which works. This act can cause losses for businesses in terms of funds and reputational damage.
Here, we explore what a BIN attack is, its effect on businesses, and how to prevent it.
What is a BIN Attack
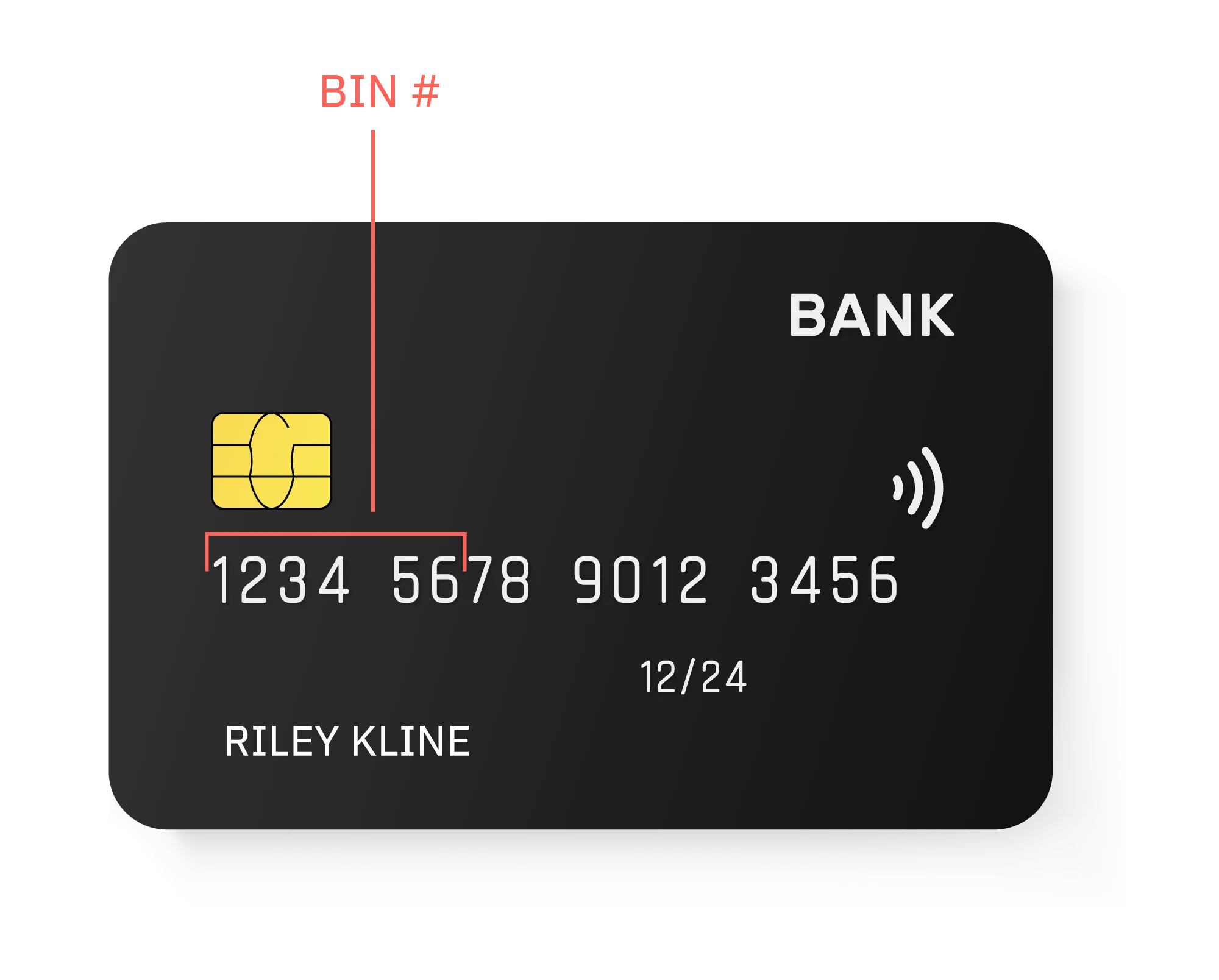
A BIN attack is an act of guessing an accurate combination of a debit or credit card number, Card Verification Value (CVV), and expiry date using brute-force computing. Once this has been completed and the fraudster acquires the right information, they use the card to commit fraudulent transactions.
While this is really a form of credit card payment fraud, this version is called a BIN attack because the brute-force attack directly targets the Bank Identification Number (the first four to six digits of a debit or credit card).
The fraudster could theoretically attempt to guess each of the remaining numbers at a time, but this process is extremely time-consuming. In order to speed up the process, most BIN attacks rely on software such as auto-dialers that generate card combinations.
After generating a number of card combinations, the fraudster then tests them by using them on online merchants and payment gateways. At this point, they are verifying that they have a legitimate card number, and the related information they need to use it (the CVV, the expiry date, and any other information about the cardholder they can garner or guess).
In many cases, these fraudulent attempts are blocked without the cardholder ever being aware that the fraudulent activity took place.
How does BIN Attack Fraud Occur?
BIN attacks, though a new kind of fraud, takes a toll on businesses. Scammers conduct these attacks by generating thousands of possible card numbers and subsequently testing them.
At a basic level, outlined below are the steps involved in a BIN attack.
1. Targeting a bank’s BIN
The fraudster chooses a financial institution to target, and acquires their Bank Identification Number (BIN). These numbers are public knowledge, so they are very easy to acquire - and serve as an ideal starting point for someone attempting to perform a brute-force attack.
2. Generating possible card numbers with software
Since the BIN is only a portion of the full card number, the fraudster then has to generate possible account numbers for the card. While this can be done manually, typically, fraudsters employ auto-dialers and other automated systems to generate possible card numbers based on the BIN they are targeting.
Essentially, the fraudsters generate thousands of potential card combinations for the financial institution they are attacking.
3. Testing
Once the fraudsters have generated card numbers, they need to test to ensure that the credentials work and they can complete a purchase. Essentially, they are verifying which cards can be used for fraud. The fraudster will perform a series of small transactions with each number until they succeed.
In some cases, fraudsters will actually operate a fraudulent store, where they can perform test transactions.
4. Storage
Once a card is successfully used to make a fraudulent transaction, the fraudsters store the information so they can make further fraudulent transactions with it. The idea being that once they’ve tested that the card works and have the proper credentials, they can begin to commit fraudulent transactions freely.
The fraudster continues to commit fraud using the stolen credentials until the card is canceled or the authentication credentials are changed.
Impacts of BIN Attacks on Businesses
A BIN attack is a type of card not present fraud because it’s conducted without the card being physically present to authorize the transaction.
Just like any other fraud, BIN attacks have several effects on businesses globally. This attack doesn’t just make businesses lose funds but also affects their public reputation. Financial institutions, online merchants, and payment gateways are among the businesses targeted by brute-force attacks.
Below are some of the effects BIN attacks have on businesses:
- Increased Chargebacks: This happens when a charge is repaid to a payment card issuer should a customer successfully disputes a transaction on their statement. When fraudsters conduct card tests on online merchants, these platforms will likely pay chargebacks out of their purses while the issuer doesn’t. This also leads to the company incurring additional expenses and recording increased disputes.
- Reputational Impacts: Online merchants and financial institutions risk tainting their image when they are affected by BIN attacks. When cardholders see the name of a merchant or payment gateway on their statement concerning a fraudulent transaction, they become wary of such a platform.
The effect is far-reaching for payment gateways as they are expected to comply with regulatory laws by preventing BIN attacks. Should these platforms fail to forestall brute-force attacks, they are likely to be viewed as incompetent.
- Regulatory Fines: Payment gateways and merchants whose platforms are often used by fraudsters to test cards can be fined by regulatory authorities or may risk losing operation licenses. These fines could have negative effects on the platform’s revenue.
- Strain in Partnerships: Successful BIN attacks can cost businesses a lot in terms of growth and partnerships. For instance, if a bank identifies a merchant as one where cards are often being tested, they might choose to terminate every business relationship with such platforms.
5 BIN Attack Prevention Methods & Best Practices
Interestingly, cardholders and financial institutions can’t stop fraudsters from guessing credit card numbers and running card testing fraud using the BIN of a target bank, however, the resulting transaction attempts can be blocked without the cardholder noticing any activity.
While some businesses still rely on manual approaches, others now use best practices to protect themselves, business partners, and clients. To help organizations prevent BIN attacks, we outline and explain the top five prevention methods below.
1. User Identification
This is the act of conducting verification checks to be sure customers are who they claim to be. This process is the first stage in combating many types of fraud - including BIN attacks.
Ensuring customers meet KYC requirements, as well as performing customer due diligence and enhanced due diligence are some strategies businesses use to ensure their customers are legitimate. However, user identification alone doesn’t prevent BIN attacks.
2. Limiting Multiple Checkouts, Especially Those With Strange Addresses
As stated earlier, BIN attacks are characterized by low-value transactions which the scammer attempts in a short period. Limiting the number of checkout attempts for a single user may be a step in the right direction.
Additionally, fraudsters are likely to fill in the wrong address and ZIP codes during checkout. Implementing an AVS to check if the address and ZIP code used by the scammer match that of the card is a great method for protecting against BIN attacks - and the card testing fraud that follows.
3. Transaction Monitoring and Analysis
Fraudsters are quite sneaky and may have tools to help them bypass user identification. This makes transaction monitoring and analysis one of the best practices to prevent BIN attacks.
Since BIN attacks involve a high volume of low-value transactions, monitoring transactions for suspicious activity is one of the first - and best - places to look for BIN attack fraud. Organizations should look specifically for a high volume of low-value transactions, as card testing is a major component of BIN attacks. In fact, if you can catch fraudsters at this point in the process, you can often stop them from committing larger purchases with the card (after they’ve tested that it works).
Don’t just monitor for cardholders with frequent transaction patterns, but also look for recurring expiry dates and CVV errors - especially when tied to the same card. This can be a red flag of card testing and could signal a BIN attack.
4. Activity and Event Monitoring
While transactions are the first place you may think to look, it isn’t the only place to watch for BIN attacks. However, there is a lot more that can be used to identify - and potentially prevent - BIN attacks (and the fraud that follows).
Activity and event monitoring empowers risk teams to monitor user behavior and actions taken outside of transactions. While transactions themselves are a great point of analysis, other signals can be used to identify suspicious behavior, or signal that fraud is about to occur.
Using activity monitoring, teams can analyze logins, account changes, IP addresses, and devices used to detect irregularities that could signal fraudulent activity like BIN attacks. These can then be flagged for further investigation or stopped on the spot.
5. User Authentication
This is a protective measure that adds an extra layer of security to an online merchant store or financial services platform. Platforms that lack this feature can be a soft target for fraudsters and likely translate to the success of BIN attacks.
The majority of brute-force attacks use software programs that rapidly test card numbers alongside their other credentials. Using systems that validate the authenticity of a user at the point of a transaction is an essential protective measure that can actually prevent BIN attacks from occurring in the first place. These systems can identify whether the user is a human or a software bot using solutions like CAPTCHA. Multi-factor authentication solutions such as biometric verification, facial recognition, and more are great ways to validate that a user is the account holder before authorizing a purchase.
Limit BIN Attacks with Unit21
A BIN attack is a specific kind of fraud that isn’t easy to detect and block in real time. Because fraudsters conduct these attacks in a similar fashion, risk management teams need to know what red flags—including non-monetary ones—to look out for.
By understanding how BIN attacks work, risk teams can develop rules to detect and prevent this fraud in real time.
Learn how Unit21 can help you limit losses and reputational damage from BIN attacks by scheduling a demo today.

