
Identity Verification
How to Use It to Prevent Fraud & Money Laundering
An essential part of combating fraud, money laundering, and other financial crime is making sure customers are truthfully representing themselves.
That means checking to see if a client’s credentials refer to not only an actual person, but also the same person who is presenting them. This process of identity verification is a critical first line of defense, as criminals often try to obfuscate their true identities in order to make it difficult to trace crimes back to them.
We’ll discuss what identity verification is, why it’s an especially critical process in the world of finance, and how to build an effective identity verification program for your financial institution.
What is Identity Verification?
Identity verification is the process of determining whether a person’s identity credentials correspond to a real person, and accurately match the appropriate person. In finance, it’s meant to prevent the use of forged identities to commit fraud, money laundering, and other financial crimes.
What is Digital Identity Verification?
Digital identity verification refers to computer-driven methods used to automatically (and sometimes remotely) authenticate a person’s identity. It is often used for online identity verification when a person or their ID documents are not physically present.
Places that deal with high volumes of people needing to have their identities checked, such as airports, may also use digital identity verification software to speed up the process.
Why Identity Verification is Important in Financial Services
Identity verification is critical in the financial world because it’s a key process in combating financial crime. On a smaller scale, it helps to prevent various forms of fraud such as credit card cloning and synthetic identity theft. On a larger scale, it helps to trace money that’s moved across borders and between corporations to ensure it isn’t being laundered.
Identity verification also helps to decrease the risk involved in financial transactions. On one hand, financial institutions can trust that customers are who they say they are and are acting in good faith. On the other hand, customers can feel confident that their financial institution is taking appropriate steps to ensure their money isn’t stolen or illegally sourced.
Finally, not following KYC identity verification regulations can result in steep fines. Beyond paying a monetary penalty, though, an institution can suffer damage to its brand reputation if its failure to comply is publicized. This often creates distrust among both potential and existing customers, leading to the institution losing business.
Identify Verification vs. Identity Authentication
Identity verification and identity authentication are related terms, though they refer to slightly different processes.
Identity verification is more about ensuring the credentials of a customer being onboarded correspond to a real person or company.
Identity authentication, meanwhile, deals with ensuring that an existing customer involved in a transaction is actually that person or company, as opposed to someone pretending to be them.
How Identity Verification Works
Digital Identity Verification Methods to UseOn a general level, identity verification works by collecting someone’s ID credentials and comparing them with records that trusted institutions (such as governments) already have on file. Verified credentials can then be kept by an institution to check if someone claiming to be the same person is, in fact, that person when they initiate a transaction. Here’s a bit more detail about how it all works.
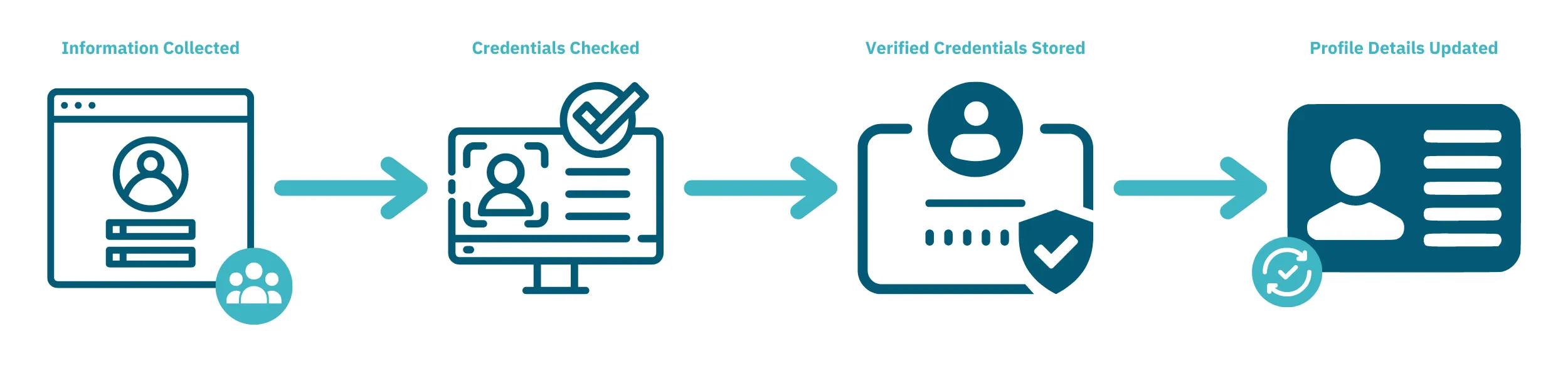
- An institution collects identifying information on not only the legal representative of an account and its assets but also any beneficial owners. This can include those people’s full names, birth dates, home addresses, citizenship, or any other information that can be used to identify them with a federal government (SSN, passport, etc.).
- Next, the institution checks sets of identifying information against trusted sources that can corroborate individuals’ identities. These can be government databases or pre-vetted lists included in anti-fraud/AML solutions. They can even be credentials on file with other organizations a person may have interacted with, including personal websites or social networking sites.
- If a person’s identity credentials match a real person, and correspond to the same person under scrutiny, the institution stores them for future reference. When requiring authorization for further transactions, the institution can use these details to verify if a person involved is who they claim to be.
- The institution should also update the details of a client’s identity profile when appropriate. This helps to prevent false negative authentications. Tracking these changes can also serve as potential evidence of suspicious activity.
Digital Identity Verification Methods to Use
Several identity verification services are using digital methods now. Not only are these processes usually faster, but they also work even if a person or some of their identifying credentials aren’t physically present. Here are some common ways identities can be verified digitally.
ID document
A piece of official ID (such as a passport) – or sometimes just a picture of one – is scanned to determine if the document is legitimate. If the person represented by the document already has information on file, the credentials on the document can also be checked to determine if it’s the same person. This is a quick and simple way to digitally verify someone’s identity.
Biometrics
A scanner or piece of software reads measurements of a person’s bodily features that uniquely identify them. Fingerprints are commonly used, but videos that can be analyzed for facial features or voice patterns are also options. Biometrics are often combined with ID documents to ensure the person presenting the document and represented on the document match.
Liveness detection
An advanced form of biometric identification that uses motion detection to verify whether a person’s credentials are genuine. Their bodily functions may be measured, or they may be asked to perform specific actions in a video. This makes liveness more difficult to fake than static pictures or videos.
Knowledge-based authentication (KBA)
A customer is asked questions about the information already on file to verify their identity. There are two general types of KBA: static and dynamic.
Static KBA is based on a list of questions agreed upon ahead of time. It’s typically not very secure because the answers can be guessed by knowing or researching enough about someone.
Dynamic KBA is based on questions about a customer’s past transactions with an institution. It tends to be more secure because the answers are specific to the customer-institution relationship, as opposed to knowledge that may be publicly available or garnered through phishing (or similar scams).
Information footprint analysis
An institution verifies a customer’s credentials by comparing them against other sources the customer has interacted with. These can include things like social media account profiles, or reports from credit check companies. This method is useful if the customer doesn’t have a long transaction history with the institution yet.
One-time passcode (OTP)
A method of multi-factor authentication in which a customer wanting identity verification must also input a randomly-generated passcode or click a URL. This is generated and sent to the customer via text message or email and expires after a certain amount of time. This adds a layer of security over a static password by requiring access to a device or account that only the customer should have access to.
Trusted identity network
This form of identity verification works by leveraging the verification process of another institution. A common example is the ability to use the login credentials for an email or social media account to gain authorization for an institution. The email or social network provider has a trusted enough identity verification process that other institutions will simply piggyback off.
Identity Verification Scams and Schemes to Watch Out For
While different forms of identity verification have their advantages, they also have vulnerabilities that are important to be aware of. Here are some common identity verification scams that criminals will use to try and circumvent authorization processes.
Stolen ID scans
Criminals can steal people’s ID documents and create scans of them. This allows a fraudster to present themselves as a legitimate person, even though they’re not the same person as the one on the ID document.
Certain documents have special security features that make them more difficult to replicate through scans. This scam can also be averted by requiring other types of verification, such as biometrics, in addition to ID documents.
Fake biometrics
Though more difficult than faking an ID document, scammers can also spoof biometrics in checks requiring pictures or videos. They can use masks or photos of photos; image and audio editing software; and even deepfake technology to look and sound like a particular person. This is why liveness detection is sometimes used: to see if the person is capable of following spontaneous instructions, which a pre-recorded video can’t do.
Hacking, phishing, and snooping
Criminals can break passwords on online accounts to access them and learn people’s private information. Or they can use phishing scams to trick people into revealing sensitive information. They can even simply look around on a person’s website or social media profiles for personal details that might serve as answers to security questions. Then they can use this data to fool identity checks or sell it on the black market to someone looking to do so.
This is why it’s often better to use dynamic KBA instead of static KBA. It’s also why identity verification methods that rely on things a person has (e.g. ID documents) or that are inherent to them (i.e. biometrics) are usually more secure than those that rely on a person simply knowing something.
Stolen or synthetic identities
A criminal who can steal someone’s identifying information, or gain control of one or more of someone’s online accounts, may attempt to pass themselves off as that person. A fraudster may also piece together stolen personal details from various people. This creates an identity profile that contains legitimate information but doesn’t correspond to a single real person.
These schemes can cause problems for identity verification methods that rely on information or authorizations from trusted third-party sources. That is, it becomes difficult to know if the person presenting the credentials is actually the person the credentials represent. So it can be useful to employ biometrics or multi-factor authentication as additional checks.
And these threats are only getting worse with the use of AI and machine learning technology like deep fakes. Fortunately, we've got a list of strategies to use to combat compromised and synthetic IDs that are leveraging AI and machine learning tech.
SIM swapping
This is an identity theft scheme that targets mobile phones. It involves a fraudster acquiring a person’s identifying information, then using it to fraudulently ask the victim’s phone service provider to transfer the victim’s phone number. The phone number becomes registered with a phone the criminal owns, allowing them to intercept the victim’s phone calls and text messages.
This scam has become popular recently as a way of bypassing some forms of multi-factor authentication. For this reason, some institutions opt to use alternative options to passcodes sent via phone calls or text messages as additional authentication factors. These include one-time URLs sent through email, codes generated by physical security tokens, or specialized authentication applications.
Identity Verification Best Practices to Follow
Identity verification isn’t a “one size fits all” process; there are many different ways to go about it. However, there are a few general points that financial institutions should consider on their way to assembling effective identity verification programs.
Assess the institution’s current average risk profile
The first thing a financial institution should do is look at the overall level of risk in its current operations. For instance, the services it offers may make it more vulnerable to certain types of financial crime than others. Also, depending on their demographics, existing customers may present a greater risk of being victimized by financial crime (e.g. seniors) or of perpetrating crime themselves (e.g. foreign nationals).
Choose/build an appropriate identity verification system
There are several different methods of verifying a customer’s identity, each with its pros and cons. Once a financial institution works out the relative level of risk it’s dealing with, it can choose an identity verification service (or suite of services) that conforms to those requirements.
Educate customers
If a financial institution is transitioning over to new identity verification methods, it should advise its clientele ahead of time. In any event, they should make training materials available that explain how to use the available identity verification methods. They should also have customer service representatives who are very familiar with the system(s) in use, ready to assist any clients having difficulties.
Evaluate individual client risk
Part of verifying a customer’s identity is comparing their credentials against databases regarding risky or illegal activities – a process known as name screening. If someone has a history of involvement in politics, run-ins with the law, or other shady dealings, they are more likely to be involved in financial crime going forward. This allows a financial institution to properly allocate its KYC resources, such as requiring more frequent and thorough verification for higher-risk clients than for ones that pose low risks.
Keep up-to-date records of verified identities
Once a financial institution has an accurate record of a person’s vitals and background, they need to maintain and update it whenever appropriate. There are two reasons for this. The first is that building up a history of a customer's activities and changes makes it easier to spot what is or isn’t “typical” financial behavior for them. Additionally, this “paper trail” serves as evidence of an identity verification system in action if concerns about regulatory compliance arise.

