
Card Cloning
Meaning, Examples, & How to Prevent It
Increasingly, people use credit and debit cards to store and transmit the information required for transactions. As an illustration, the world’s top 6 credit card brands (Visa, UnionPay, Mastercard, American Express, JCB, and Discover) accounted for over 440 billion purchase transactions worldwide in 2019.
Unfortunately, this makes these cards attractive targets for criminals looking to commit fraud. One way they do so is through card cloning.
Here, we’ll cover what card cloning is, how it works, and how to prevent it.

What is Card Cloning?
Card cloning is a type of fraud in which information on a card used for a transaction is covertly and illegally duplicated. Basically, it’s a process thieves use to copy the information on a transaction card without stealing the physical card itself.
This information is then copied onto a new or reformatted card, allowing criminals to use it to make fraudulent purchases or gain unauthorized access to a person’s accounts.
The most widespread version is credit card cloning, though debit card cloning is also common. Any type of card that can be used to authorize a payment or account access – even a gift card – could be a target for card cloning.
How Does Card Cloning Work?
The most common form of card cloning is known as “skimming” and generally works like this:
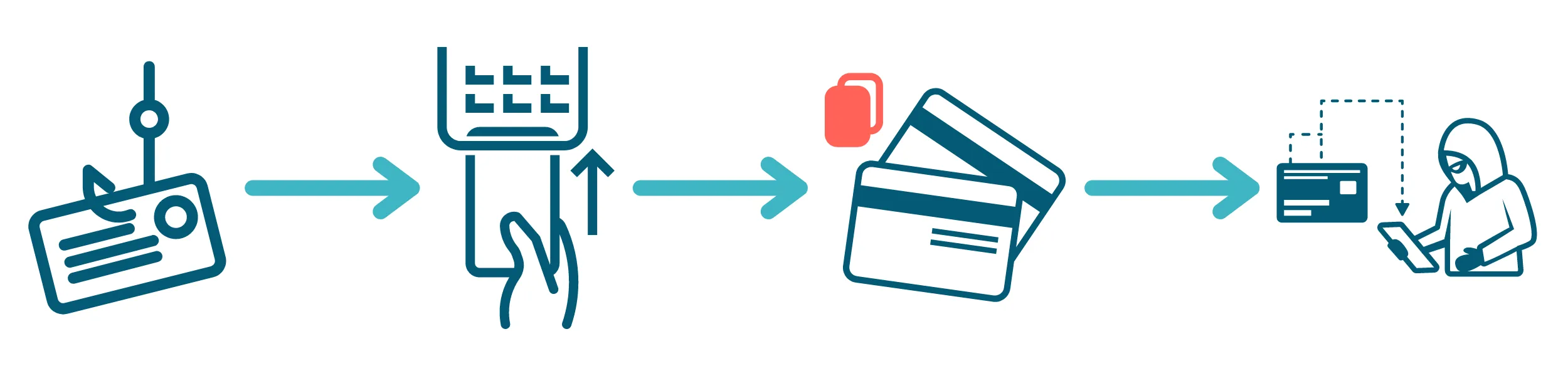
- Criminals install a “skimmer” – a credit card cloning machine that secretly reads and copies card information – in an ATM or point-of-sale terminal.
- A customer’s card is fed through the card reader on the ATM or POS device (to facilitate the transaction) and the skimmer (to copy the card’s information).
- The criminals retrieve the information copied by the skimmer.
- The criminals can then use the stolen information as-is to commit fraud, copy it to a fabricated or stolen card (i.e. card cloning), and/or sell it on the black market.
So how does card cloning work in a technical sense? Payment cards can store and transmit information in several different ways, so the tools and methods used to clone cards can vary depending on the situation. We’ll explain below.
Magnetic Stripe

Most payment cards have a magnetic strip that runs along the back. This strip stores and transmits analog transaction information, in much the same way as a cassette tape stores an audio signal.
Unfortunately, this method offers no encoding protection, so it is easy to clone magstripe-only cards using even a rudimentary skimming machine. That’s why these types of cards are being phased out in many places.
EMV Chip
An EMV (Europay, Mastercard, and Visa) chip is a microchip installed in newer payment cards. It dynamically encrypts each transaction made with the card. This makes it difficult to access the actual authorization information, even if a criminal attempts to clone the card.
It’s not foolproof, though. Thieves have developed devices called “shimmers” that operate in much the same way as skimmers, but work on cards with EMV chips. They have also figured out how to transfer the digital information on an EMV chip to an analog magnetic strip. This effectively clones the card while bypassing the security provided by the EMV chip.
Contactless Tap

The newest payment cards are equipped with radio frequency identification technology (RFID). This allows them to transmit transaction information to a card reader simply by being nearby, without physically inserting the card in a slot. This helps to avoid skimmers and shimmers but is still not without its vulnerabilities.
Criminals have developed an RFID-enabled card cloning device they can conceal on their bodies while walking down the street. This allows them to steal information from RFID-enabled cards just by being in close enough proximity to their owners.
How Card Cloning Fraud Works
Most credit card cloning fraud is done through the use of skimmers. Skimmers read credit card information such as numbers, PINs, CVV data through the magnetic stripe, and can be attached to hardware such as point of sale (POS) terminals, or ATMs, allowing them to steal whoever uses that hardware’s information.
Criminals can also create a faux keypad on POS terminals or ATMs that allow them to steal PIN information.
Once the information is stolen, the criminal can then make a physical credit card linked to another person’s money. The original cardholder may not even realize that this has happened, however, it is possible to tell by looking at their financial statements, bank accounts, or by seeing if their credit score has changed.
Examples of Credit Card Cloning Fraud
There are several ways to capture the information needed to make a cloned card. A thief may simply look over someone’s shoulder to learn their card’s PIN, or use social engineering tricks to coerce a person into revealing this information. They could also install a fake keypad on an ATM or point-of-sale device to copy the PIN of anyone who inserts a card.
Here are some common card cloning scenarios.
1. Point of Sale (POS) terminal skimming
Criminals attach a skimmer device to a merchant’s point-of-sale device, sometimes as easily as plugging it into a USB port. To make things even easier, they may recruit one of the merchant’s employees or technicians to install the skimmer and retrieve the stolen data for them.
Then, when a customer swipes their payment card through the machine, the skimmer copies their card details. This information is then relayed to (or downloaded by) thieves, who use it to clone cards and then make fraudulent purchases or steal money from bank accounts.
Some creative fraudsters are modifying fake POS terminals to have the credentials of real merchants. Then they conduct fraudulent return transactions to load gift cards or debit cards, then cash out the stolen money at ATMs.
2. ATM skimming
Fraudsters use skimmers at ATMs to capture information off bank cards in order to illegally access other people’s bank accounts.
Usually, the skimmer is placed over the top of the original card reader but is so similar in size, color, and texture that it’s challenging to detect. The skimmer could also be installed inside the terminal, or along exposed wiring.
Criminals may also install a tiny hidden camera in the front of the ATM, or nearby in view of the keypad so that they can record a victim’s bank card PIN. Alternatively, they may install a fake keypad on top of the original keypad to record a victim’s key presses, thereby stealing their PIN.
3. Fuel pump skimming
“Pay at the pump” is expected at major branded gas stations, and fraudsters are taking advantage of that to clone cards. Often, the skimmer they install will be within the internal wiring of the payment processing machine, so customers won’t know that it’s there.
For this reason, it can be safer to just pay the store attendant with cash, rather than using a credit or debit card at the register or the pump.
How To Prevent Card Cloning
Unfortunately, it is likely impossible to eradicate card cloning fraud. Even now, criminals are finding ways to breach the most current card security standards. So the best approach when it comes to preventing card cloning is a comprehensive risk management strategy.
1. Use and invest in new card security technologies
New security standards like EMV chips and RFID technology make it harder for criminals to clone cards. The implementation of Europay, Mastercard, and Visa (EVM) chips has been one of the biggest advancements in the fight against card cloning since they are safer alternatives to magnetic stripes. They use payment information that is encrypted to make it exceptionally difficult for criminals to clone cards, but EVM chips still have their vulnerabilities.
Even if their cards have EVM, people are more likely to use the magnetic stripe at POS terminals due to the familiarity allowing their credit card information to potentially be stolen. Also, a recent study from a security firm stated that cybercriminals have found a method to make purchases with a magnetic stripe card using data that was meant for EVM chips.
This gives insight to the upsetting reality that is: it is almost impossible to get criminals to stop cloning cards because they will always try and find a workaround, so this should be just one part of an effective strategy to combat card cloning.
2. Review transaction infrastructure
Companies, especially financial institutions, should periodically take stock of the points at which they take card transactions, such as ATMs and point-of-sale machines. They should secure these points to make it more difficult to clone cards.
For example, making sure that POS terminals are all EMV compliant as well as helping customers purchase things in a more secure manner are a few ways Merchants can help make it more challenging for criminals to clone cards.
Despite possibly being impossible to end card cloning, the combination of customer profile data, securing physical infrastructure as well as EMV chips can help banks and merchants be more confident that the cards that are being used aren’t cloned cards, but instead, are the actual, legitimate, ones.
3. Educate the public
Consumers should be made aware of how card cloning works, how big of a threat it is, and how they can protect themselves. Offer tips such as:
- Check card readers for bulk or other suspicious traits before inserting your card
- Monitor your financial accounts and set up suspicious activity alerts
- Use ATMs associated with banks whenever possible
- Use EMV chip readers or contactless payment whenever possible
- Contact your bank or card provider immediately if you think your card has been cloned
4. Build customer profiles
Analyzing a customer’s transaction data – now often done through machine learning – can reveal patterns in how they use their card. These include:
- Where they live
- What businesses they frequently visit
- Which transmission method (magstripe, EMV chip, or contactless pay) they typically use
- How often they use their card
- How much they spend, on average, per card use
- What time(s) of day they tend to use their card
These traits can be used as a baseline for what “normal” card use looks like for that customer. So if a transaction (or series of transactions) shows up on their record that doesn’t match these criteria, it can be flagged as suspicious. Then, the customer can be contacted to follow up on whether the activity was legitimate or not.
Quickly Detect and Respond to Card Cloning Fraud with Unit21
Card cloning fraud can’t be stopped by new security technology alone. Preventing it requires a multi-faceted approach that also includes educating consumers, knowing who your clients are, analyzing customer behavior, securing vulnerable contact points, and keeping an eye on financial activity.
Equip your risk and compliance teams with Unit21’s transaction monitoring solution that puts them in control with no-code rule definitions and detection workflows. To see it in action, book a demo with us today.
