
Name Screening
How It Works & Best Practices
One of the challenges for financial institutions is assessing how much financial risk each customer represents, both during onboarding and when performing ongoing due diligence.
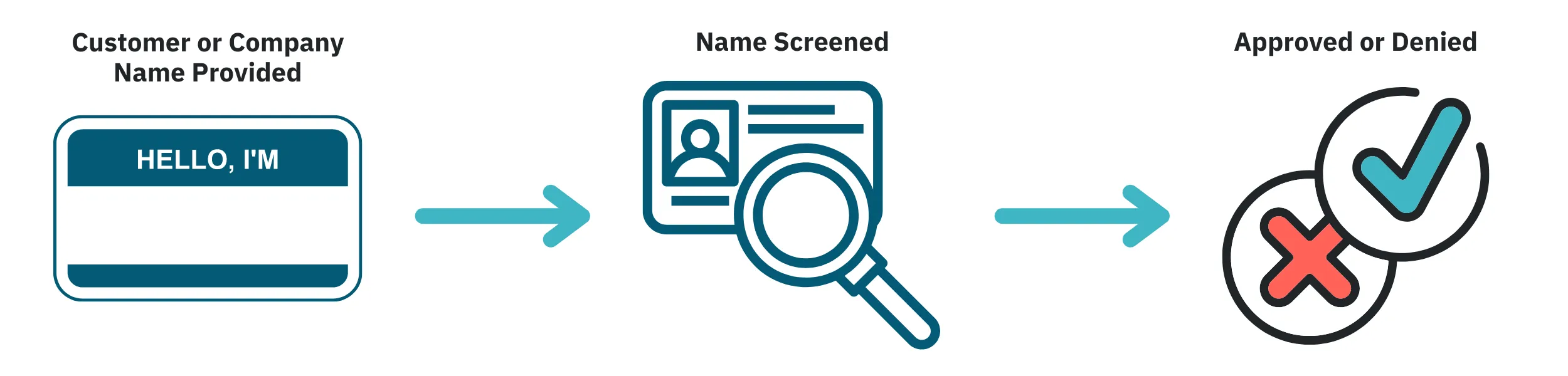
Name screening helps with this by checking a customer’s identity against official sources, denoting sanctioned, prohibited, or otherwise high-risk individuals and companies.
Let’s first discuss what name screening in banking specifically refers to.
What is Name Screening in AML?
Name screening refers to searching for a person’s name and/or other personal information in databases related to financial risk. These could include sanctions lists, lists of politically exposed persons (PEPs), criminal wanted lists, or even news media (to check for negative coverage on a person).
Name Screening as a Component of KYC
Name screening in KYC (Know Your Customer) checks serves two purposes. The first is to build a risk profile of a client when a financial institution onboards them. A person holding political clout, having a criminal history, receiving unfavorable news coverage, or under international trade restrictions likely poses a higher risk of being involved in financial crime than someone without these factors. Sometimes, this risk may be too high for an institution to consider accepting a client’s application.
KYC name screening is also a component of ongoing customer due diligence. A person with several financial risk factors may not necessarily get involved in fraud, money laundering, or other crimes.
However, their profile still warrants monitoring their transactions more closely for any sign of suspicious activity. Also remember that a person’s financial risk profile may change if they gain or lose one or more risk factors, such as being elected or appointed to a prominent political position.
Name Screening Process: How It Works
Name screening in AML begins with, obviously, a person or company’s name. But even this primary step can have several complications. A person or business could have a name that is:
- common and shared with a number of other customers
- spelled or stylized differently, depending on the region or data source
- a nickname or alias that may intentionally mask their true identity
- spelled incorrectly, likely due to human error
A process called “fuzzy matching” can somewhat compensate for this by widening search parameters to include names that may be misspelled or stylized differently. But it may also pick up on people totally unrelated to the current scenario.
That’s why it’s important to have high-quality, globe-spanning information from a variety of risk-related sources to supplement names. This allows FIs to more accurately match a name to a particular financial situation, and so determine what level of financial risk a person poses.
This is important not only for choosing whether or not to onboard someone as a new customer. It’s also critical for organizing existing clients based on financial risk, so that due diligence resources can be properly allocated (i.e. higher-risk clients are monitored more closely, while lower-risk clients may need only standard AML checks).
How Name Screening Software Can Help
A financial institution likely has thousands of existing customers, and may onboard hundreds more every day. In addition, there are numerous national and international sources of information that may indicate a client poses greater financial risk. So screening each client individually is terribly inefficient.
That’s why many companies use automated name screening tools. This helps them check several relevant databases at once during onboarding to know within seconds if a potential client is high-risk.
Many modern pieces of name screening software can also monitor sources in real-time (or close to it). This means finance businesses can know sooner about changes to an existing client’s risk profile, or other suspicious financial activity that may involve a customer.
Unit21’s Onboarding Orchestrator combines your third-party KYC and identity verification data with automation, custom workflows, through data integrations – all without needing the end user to write a single line of code. Schedule a demo to see it in action today.

