
Common Authorized Push Payment Fraud & Rules to Detect
Real-time payments (RTPs) are not new but have been growing in popularity, thanks to more countries integrating their RTP systems into their national payment networks. It’s predicted that RTPs will reach 511.7B of global transactions by 2027 - up from 195.0B transactions in 2022.
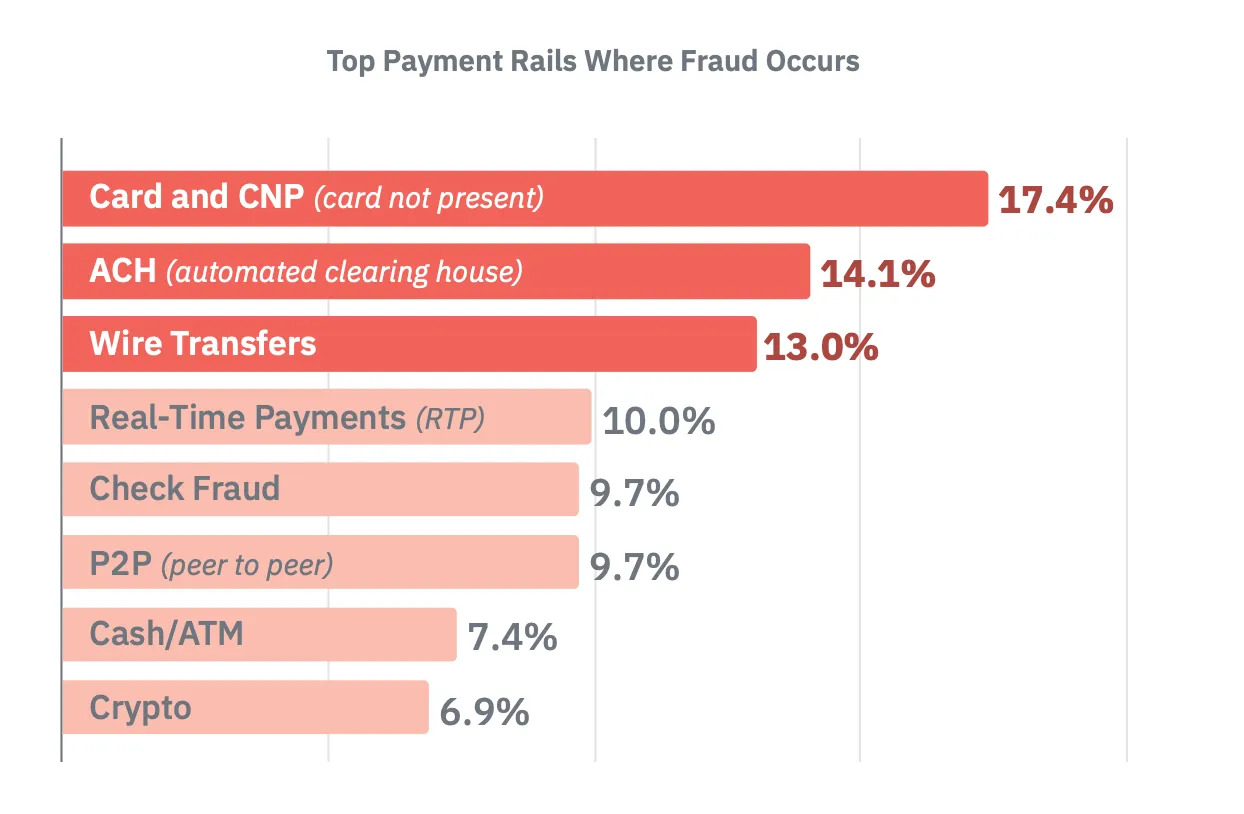
As the RTP landscape grows, fraudsters are shifting their attacks toward where these payments are - the real-time payment rails. In fact, RTP now ranks fourth in the top payment rails where fraud occurs). The reasons RTPs are attractive to legitimate users make them attractive to fraudsters; they’re processed and settled instantly, giving recipients immediate access to the money. But an added bonus for fraudsters is that payments are irreversible. This is why real-time monitoring (RTM) has become so important for fraud fighters.
In this six-part blog series, we will explore different types of fraud, how adopting an RTM system that can keep pace is a highly powerful tool in each scenario, and specifically, which rules are effective in fraud detection and prevention.
Authorized Push Payment (APP) Fraud on the Rise
The leading threat for real-time payment rails is APP fraud. ACI Worldwide released a report that found the CAGR of APP scams value compared to the CAGR of real-time transactions value (2022-2027) is 9% vs. 41%!
APPfraud is largely conducted through social engineering and other forms of deception to trick someone into sending money to someone illegally acting as a legitimate recipient. It is especially appealing to fraudsters because the payment is authorized, raising fewer red flags for financial institutions, and it settles instantly, giving immediate access to funds with payment being irreversible by both the victim and the financial institution. Typically, fraudsters employ impersonation techniques to pose as a legitimate person or institution, adding credibility to their scam.
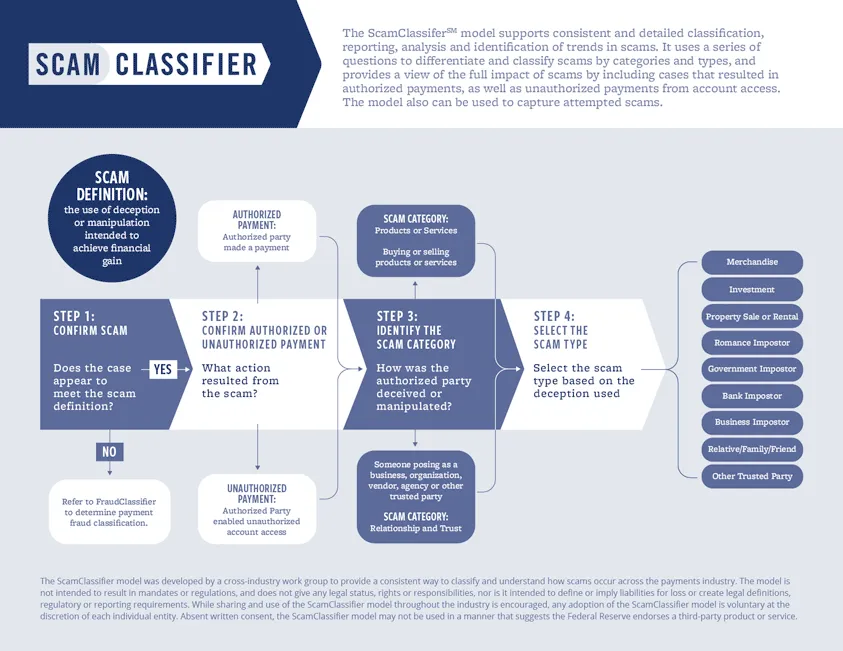
Below is a good infographic on how to determine different types of categories and scams based on several strong indicators.
Common Types of APP Fraud
Fraudsters commonly impersonate legitimate people or institutions that add credibility to their scam. They will use personal information obtained through illegal means like phishing or hacking to further lend authenticity to their scams.
Some common forms of APP fraud include, but are not limited to:
- Business Email Compromise (BEC) - Fraudsters impersonate a company executive or a trusted vendor to trick employees into making payments to a fraudulent account.some text
- Example: A finance employee receives an email that appears to be from the CEO requesting an urgent wire transfer to a supplier.
- Invoice fraud - Fraudsters send fake invoices to businesses, impersonating legitimate suppliers or service providers, and requesting payment to a fraudulent account.some text
- Example: A company receives an invoice for services rendered from a familiar supplier, but the payment details have been altered to the fraudster's account.
- Romance scam - Fraudsters create fake online profiles on dating sites or social media to build romantic relationships and manipulate victims into sending money.some text
- Example: A victim believes they are in a relationship with someone they met online, who then requests financial help for an emergency.
- Investment scam - Fraudsters convince victims to invest in fake investment opportunities, promising high returns.some text
- Example: A victim is persuaded to transfer funds to invest in a non-existent high-yield investment program.
- CEO fraud - Similar to BEC, fraudsters pose as a high-ranking executive and instruct employees to make urgent transfers for various plausible reasons.some text
- Example: An employee receives an urgent email from the “CEO” asking for a payment to be made to a new vendor.
- Lottery & prize scams - Victims are informed that they have won a lottery or prize but must pay a fee to claim itsome text
- Example: A victim receives a notification that they have won a large sum of money in a foreign lottery and needs to pay a fee for processing.
Learn more about APP fraud, signs to look for, and steps to take to prevent it.
Effective RTM Solutions & Rules to Detect APP Fraud
Traditionally, transaction monitoring systems were designed to alert on an activity that wasn’t made by the customer, i.e., out-of-pattern transactions that are not normal for the customer. With APP fraud, this gets more complicated as the customer is the one who makes the transactions, and in the beginning, they might appear legitimate.
Effective RTM solutions have rules to detect suspicious behavior or behavioral anomalies that flag suspicious-looking transactions. It’s important to note the use of the word “effective” - the “real-time” label means that the time period for risk teams to alert and take action on a transaction is drastically reduced. That’s why any sort of latency issues can inhibit risk teams’ ability to act, especially as transactions are settled within seconds. Effective RTM solutions can automatically take action on events. For example, Unit21’s Real-Time Monitoring solution allows organizations to evaluate transaction and action events in real-time, and to create rules that automatically block or approve events in <250 milliseconds (or hold them for manual review).
The good news is, that the window for action is also reduced on the fraudster’s side, so a robust RTM solution coupled with effective customer onboarding processes can be powerful in fighting APP fraud. However, because APP fraud has characteristics that make it harder to predict, it requires individual rules in order to flag in real-time - depending on data access as well as knowledge and expectations of customers.
The ability to flag action events as well as transaction events allows teams to block transactions that include particular non-transactional attributes, such as logins, device type, or IP address.
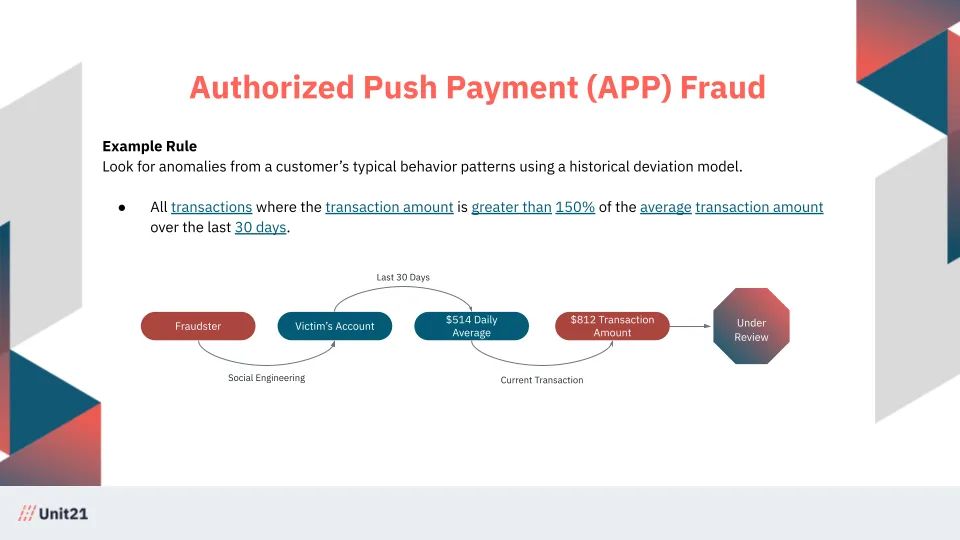
Example rule: Look for anomalies in a customer’s typical behavior patterns using a historical deviation model.
If a customer usually has transactions around $500 and suddenly that amount rises to $5,000 and to an unknown IP address at an unusual time of day, then it could be valuable to flag these types of transactions for manual review, or, depending on the appetite for risk, block the transaction pending further review.
APP Fraud in the Real World
Netflix’s The Tinder Swindler, is a good example of a romance scam and ensuing APP fraud. The docu-series follows an Israeli-born conman Shimon Hayut who posed as the son of a diamond mogul. He then uses Tinder to contact women and lavish them with expensive gifts, private jet rides, and other luxuries, using money from women he had previously conned. He would then convince the new woman to lend him money that he would never repay. It is estimated he tricked people around the world out of $10 million.
These women are not alone; the FTC noted that in 2022, reported losses hit $1.3 billion, with over 70,000 people reporting a romance scam.
When people fall for a romance scam, the world sees them as victims. The only person who doesn't view them as one is the fraudster, who sees them as an asset. Financial institutions can help protect their customers from romance scams like the Tinder Swindler by understanding the value of the asset and how fast this asset is being drained of their funds. Monitoring the frequency of outbound transactions, increasing dollar volumes per transaction, and analyzing the intended payee can help identify patterns we often see in APP fraud scenarios.
Real-Time Monitoring with Unit21
Unit21’s Real-Time Monitoring allows you to monitor events in real-time:
- Automatically take action on events - You can automatically block or approve events in <250 milliseconds, or you can hold them for review. Both transactions and actions can be evaluated in real time.
- Write, test, and deploy rules in minutes - respond to fraud faster without constant engineering support. Use out-of-the-box rules or create your own, and validate them on historical data prior to deployment.
- Allow list of good customers - Minimize the risk of flagging legitimate transactions to cut down false positives and lower operational costs.
To learn more, read our Real-Time Monitoring white paper and schedule a demo.










